Software Keepho5ll: A Detailed Guide To The Tool, And How To Use It Safely In 2026

In the digital world, new software names pop up almost every day. Some become important tools, while others leave people wondering what they are.
One name that comes up often is Software Keepho5ll.
Many people search for the software Keepho5ll loading code when they encounter it on a device, a download page, or in an old project folder.
If you have seen this term and want to know what it means and whether it is safe to use, this guide will help you understand.
The goal is to help U.S. users make informed and safe decisions about unknown software.
What Is Software Keephold?
Current information shows that Keepho5ll does not belong to any well-known program.
It is not listed in major software databases, developer networks, or trusted business directories.
This likely means one of two things:
1. It may be a small tool that only certain companies used at some time.
2. It could be a wrong name or an old file someone found.
Because it is not linked to a known vendor or developer, users in the U.S. should be careful and follow safety steps when dealing with it.
Why Does The Unknown Software Keepho5ll Need You To Be Cautious?

In the current volatile dynamics of the cybersecurity landscape, an unverified program is the source of some of the biggest threats.
In fact, even when you are dealing with software that is well-designed, they are still risky if you cannot tell where they have come from.
Therefore, I have given you the list of a few reasons why Software Keepho5ll can be a reason for concern for you:
1. Lack Of Clarity About The Creator
Do you know what the deciding factor is when you are assessing software? The developer. It’s very important to know who developed it.
Reputable software usually provides clear information regarding its developer, including:
- Credentials
- Experience
- A Way To Contact Their Support Team
Moreover, a transparent update history shows that the software is actively maintained.
Additionally, you will also get to see if it has been improved over time. Therefore, this significantly enhances user trust and security.
2. Hidden Risks In Unknown Loading Codes
It’s important to understand that unknown loading codes can pose significant dangers.
Additionally, I must also mention that scripts embedded in software can execute commands silently in the background.
They don’t need any visible indicators to the user.
So, this secretive behavior can lead to unauthorized access and data breaches.
In fact, it can even install additional malicious software. Therefore, this makes it essential to thoroughly scrutinize any unfamiliar code.
3. Potential Obsolescence Or Abandonment Of Software
You should never use software that is outdated. In fact, you must not use those that are no longer maintained.
These can expose users to multiple risks.
Older tools are frequently unable to defend against new types of vulnerabilities that cybercriminals exploit over time.
So, what happens when these function without regular updates and patches?
Then, they may find their systems vulnerable to attacks that could easily have been prevented with a more current tool.
4. Possibility Of Mislabeled Or Disguised Software
It is vital to be wary of software that may not be what it claims to be.
Some malicious programs intentionally use generic or misleading names. They do this to mask their true identity and purpose.
Additionally, this tactic is designed to trick users into downloading or running the software.
Also, this can lead to severe security breaches or harm to the user’s system.
So, you must always verify the authenticity of software before installation to mitigate this risk.
Can Software Keepho5ll Be Safe? What Are The Indications?
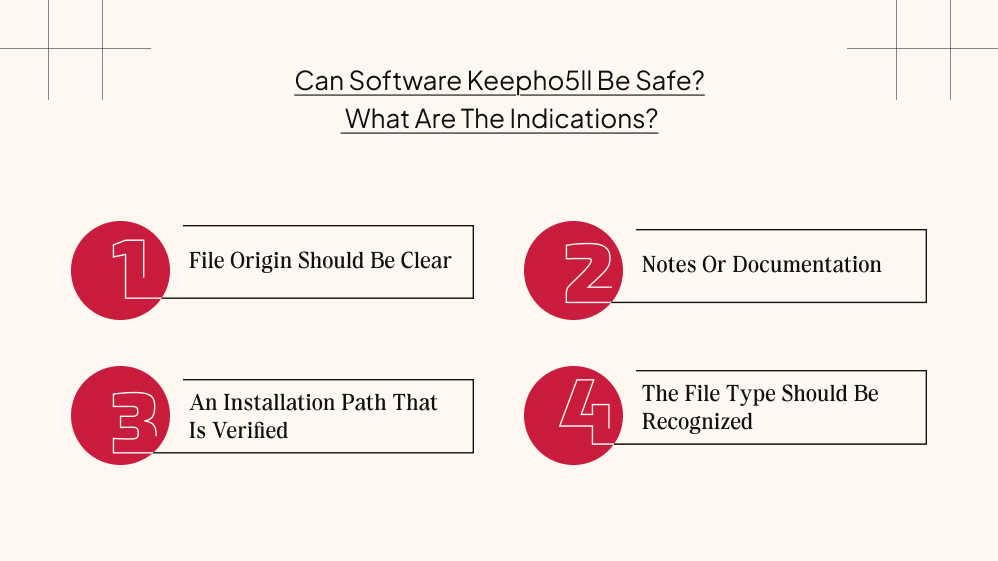
Well, if this software came from a trusty source, like a coworker, an employer, or any older project archive, then pay attention.
These are the probable indicators that will help you determine if the software is legit or not.
1. File Origin Should Be Clear
You need to know who sent you the software. Additionally, you need to be aware of why they sent this to you.
Then, this will be a strong sign that the software is safe.
2. Notes Or Documentation
When an internal tool is safe, it often carries a bunch of developer instructions with it.
In addition, some of these software also carry readme files. They increase the chances of security.
3. An Installation Path That Is Verified
Your program or the software you are dealing with should come from a verified source or path.
So, if you see any files that have a suspicious temp folder as their source, you know what to do.
4. The File Type Should Be Recognized
Files with extensions such as .cfg, .ini, .json, or .xml are commonly associated with standard configuration settings.
These loading codes play a very important role in defining the parameters and behavior of various software applications.
What Are Some Common Red Flags You Need To Watch For?

Here are potential warning signs that the software Keepho5ll might be unsafe:
1. Unknown Installation Location
Let’s say that you find Keepho5ll installed in an unfamiliar setup. Or, maybe you found this in some hidden directories on your system.
Then, it could indicate malicious behavior.
Typically, legitimate software will install in standard locations like:
- Program Files on Windows
- Applications on macOS
In addition, they will not hide in obscure folders.
2. Absence Of Version Number Or Company Attribution
Trustworthy software usually includes identifiable information. It can either be a version number.
Additionally, it can also be the name of the developing company.
If Keepho5ll does not have this information readily available, it could be a red flag.
Then, it will suggest that the software is unreliable or potentially dangerous.
3. Unexpected Loading Scripts
If the software attempts to run loading scripts that execute commands unrelated to the primary purpose you intended, it’s a significant cause for concern.
Then, this could indicate that the software is trying to perform unauthorized actions.
Additionally, it can also mean that it is trying to communicate with unknown servers.
4. Strange System Behavior
You must pay attention to any unusual system behavior after running Keepho5ll.
Additionally, you must also watch out for symptoms such as:
- Slow Computer Performance
- Frequent Pop-Up Advertisements
- Unexpected Network Activity
These may suggest that the software is causing harm or is involved in malicious activities.
How To Handle Software Keepho5ll Safely?
If you are uncertain about Keepho5ll, you can take the following safety precautions before considering its use:
1. Scan The File Before Opening
Before you open the Keepho5ll software, use a reliable and up-to-date antivirus.
Additionally, you can also go for a security program. Both of these will help you to conduct a thorough scan of the file.
This will help to identify known threats or malware.
2. Check Properties And Details
Right-click on the Keepho5ll executable file and select Properties, then navigate to the Details tab.
Here, you should look for details such as version numbers and the name of the developer.
If this information is missing or looks suspicious, exercise caution.
3. Examine The Loading Code In A Text Editor
Instead of running the loading code directly, open it in a text editor.
This will allow you to inspect the code for readability.
Additionally, I suggest that you also look for any obvious issues, such as suspicious commands that do not align with the intended use of the software.
4. Consult Your Workplace Or Team
If you’re unsure about Keepho5ll, reach out to your colleagues or IT department.
Someone may recognize the software or confirm whether it has been used in legacy systems within your organization.
5. Ensure Your Backups Are Updated
Always maintain updated backups of your important data before running any questionable software.
This way, in the event of an issue, you can restore your system to a previous state without significant loss.
6. Avoid Granting Administrator Privileges
Be cautious if Keepho5ll requests elevated access or administrator privileges.
If prompted, take a moment to pause.
Then, you must start to review the implications of allowing such access. This could lead to further vulnerabilities or unauthorized changes to your system.
What To Do If You Unknowingly Find Software Keepho5ll On Your System?
Yes, it can happen!
A lot of people have reported that they have found this software on their device even when they didn’t get it from anywhere.
So, if you find yourself in a similar situation, here’s what you are supposed to do.
- Firstly, you need to check the list of programs you have installed. If you cannot find anything substantial, you keep digging further.
- Secondly, you have to look for the unzipped folders and the recent downloads. There is a chance you have opened a package that included an extra file.
- Thirdly, you need to thoroughly review all your browser downloads.
- Additionally, you must also thoroughly go through your event logs.
- Finally, you will reach the file timestamp that will give you some important information. You will be able to identify when it appeared.
This Is The Only Guide You Need To Navigate The Software Keepho5ll Issue
With many new tools showing up online, U.S. users need clear and safe guidance.
Unknown names or characters like Keepho5ll will create uncertainty. Additionally, people often look online for answers.
A well-informed approach helps avoid mistakes, data loss, or stress.
It’s important to understand how to evaluate software, whether it is harmless or not.























Leave A Reply